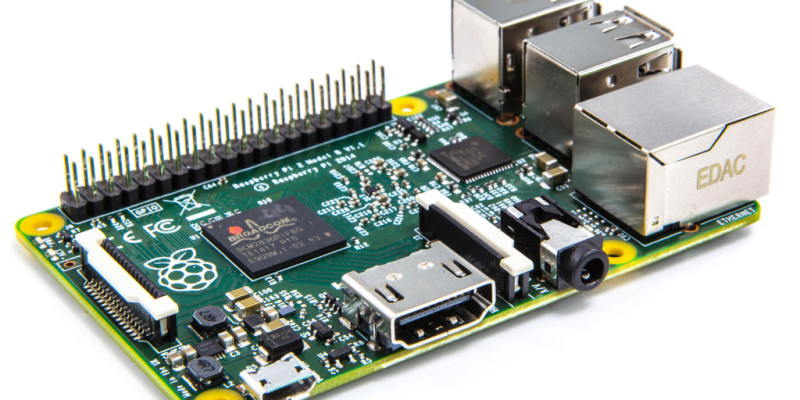
Linux is well known for its relatively high level of security, so it's big news when malware comes out to specifically target Linux. Linux.MulDrop.14 is a new piece of malware that specifically targets Raspberry Pis, to create a zombie that mines cryptocurrency for the hacker.
The malware works by infecting Raspberry Pis that use the default username ("pi") and password, targeting an open and default SSH port. Once infected, the malware will install Zmap and sshpass, change the password of the device, and configure itself to do the mining. It then scans the rest of the network for more Pis to infect, before spreading out across the web.
Once the malware has configured and setup, it will start mining for cryptocurrency. For those how are unfamiliar with how crypto-mining works, basically the software computes difficult mathematics algorithms, and once complete, the miner is rewarded in with coins of the cryptocurrency. This means that an infected Pi will be making money for somebody else, and the Pi owner may be non the wiser.
Due to the complexity of mining, the Raspberry Pi will end up running at 100% load, maxing out the Pi in both processing and power. This will hinder any running programs on the Pi, as well as adding to the Pi owner's electricity bill. Not only that, but it could end up degrading the life of the Pi, especially if it is set up for a low work-load environment (like in an enclosed space with no air cooling or heatsink).
If you don't fancy indirectly contributing to a hacker's wallet, make sure you change your Raspberry Pi's default user and password (you've done this already though right?), and change the default SSH port if you want an extra security step.